How user authentication works with Tanaza’s access points and captive portal
Tanaza is a software that allows network admins to manage user authentication in a very intuitive way through the configuration of a customizable captive portal. A captive portal is the web page people see before accessing a public Wi-Fi network, i.e. when they use the free Wi-Fi connection of a bar, restaurant, hotel, shop, etc. At first, when clients try to log in to your Wi-Fi to browse a webpage, they are unauthenticated. Being unauthenticated means that their access to your network is limited to the captive portal, other than content and services included in the Walled Garden.
To learn more about which websites and URLs are accessible by a client before authentication read this article.
On the captive portal, users can then authenticate themselves and browse the web on their Wi-Fi-enabled devices. Let’s now see the steps needed to authenticate users on a captive portal and the main login methods featured by Tanaza.
Opening of the login page of the captive portal
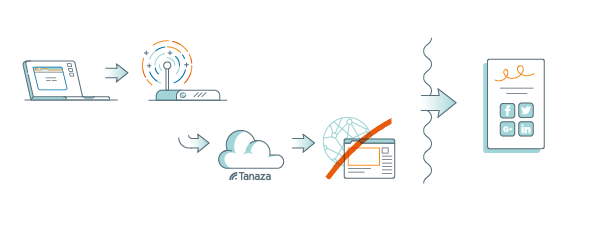
Clients’ login flow starts in this way: the unauthenticated user’s device reaches your access point and requests access to the Internet. The access point, that is connected to the Tanaza Cloud, sees the request but doesn’t recognize the client as authenticated. Accordingly, instead of showing the user a web page, it redirects the unauthenticated user to the login page, aka your captive portal. Once here, the user authenticates through the captive portal and is therefore authorized to browse the web. Now, the user can freely browse any webpage, using your Wi-Fi network.
To better understand how to use the Tanaza captive portal functionality, read this article.
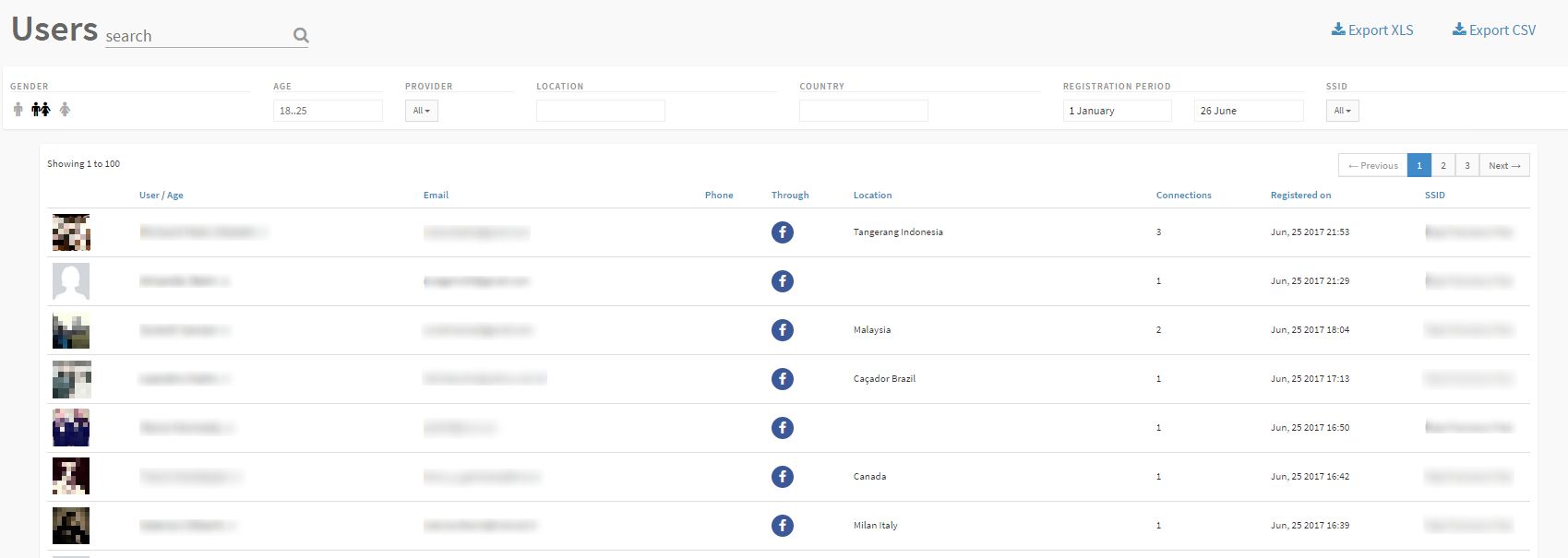
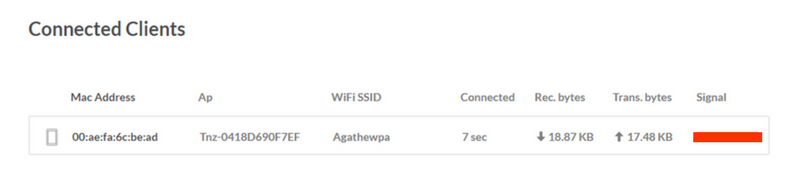
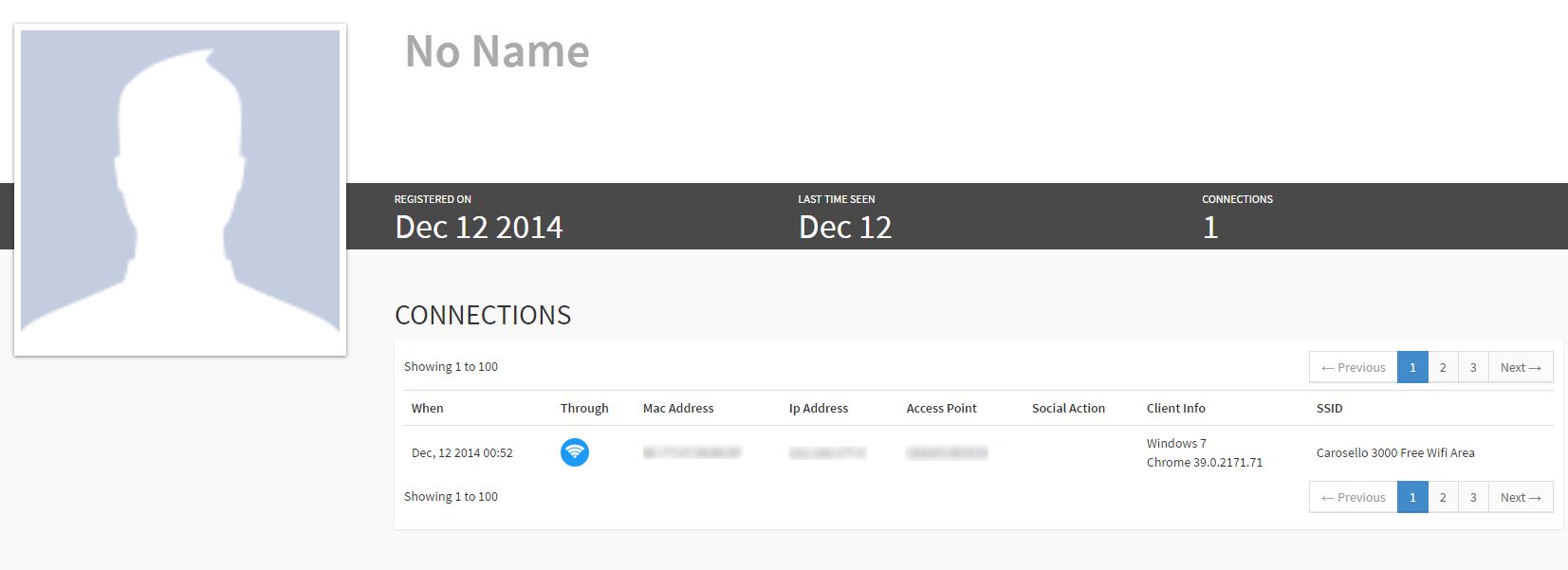
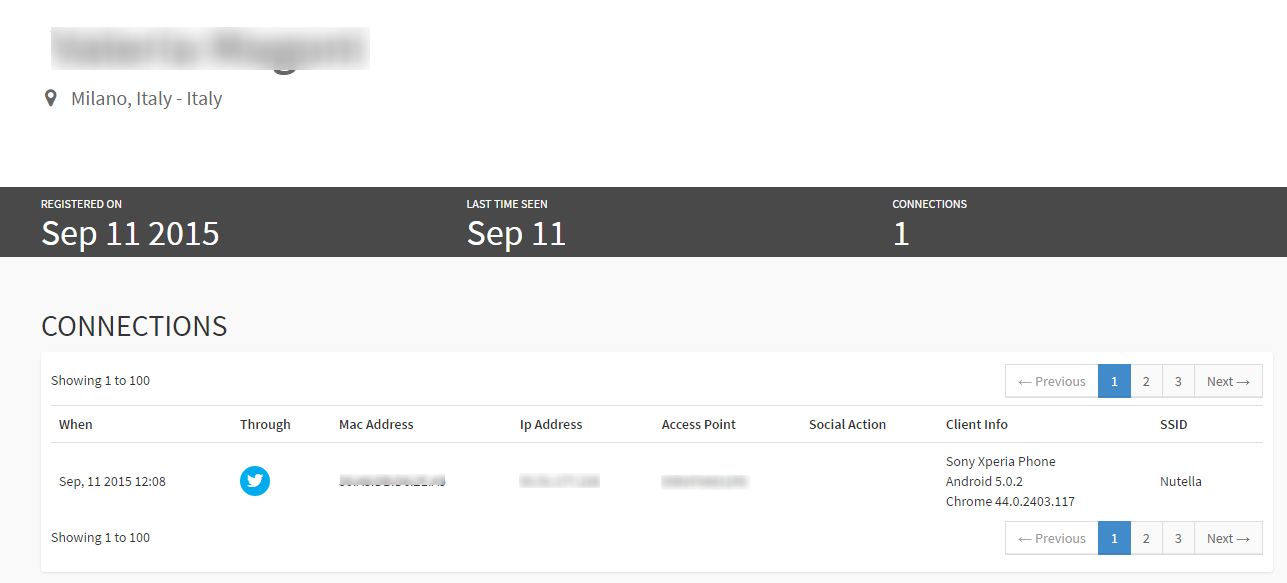
In general, network administrators cannot see the list of users connected to their network in real-time. Instead, Tanaza allows network admins to see the list of connected clients from anywhere, anytime, through a web dashboard, cloud.tanaza.com. Specifically, they see real-time users connected and authenticated (or even in the process of authenticating) through their cloud.tanaza.com management platform. Also, they see the historical data from all authenticated users, together with their personal information, in the Tanaza Analytics Dashboard. The screenshots below show how data about users and connections are viewed on the management platform of the Tanaza Analytics Dashboard.
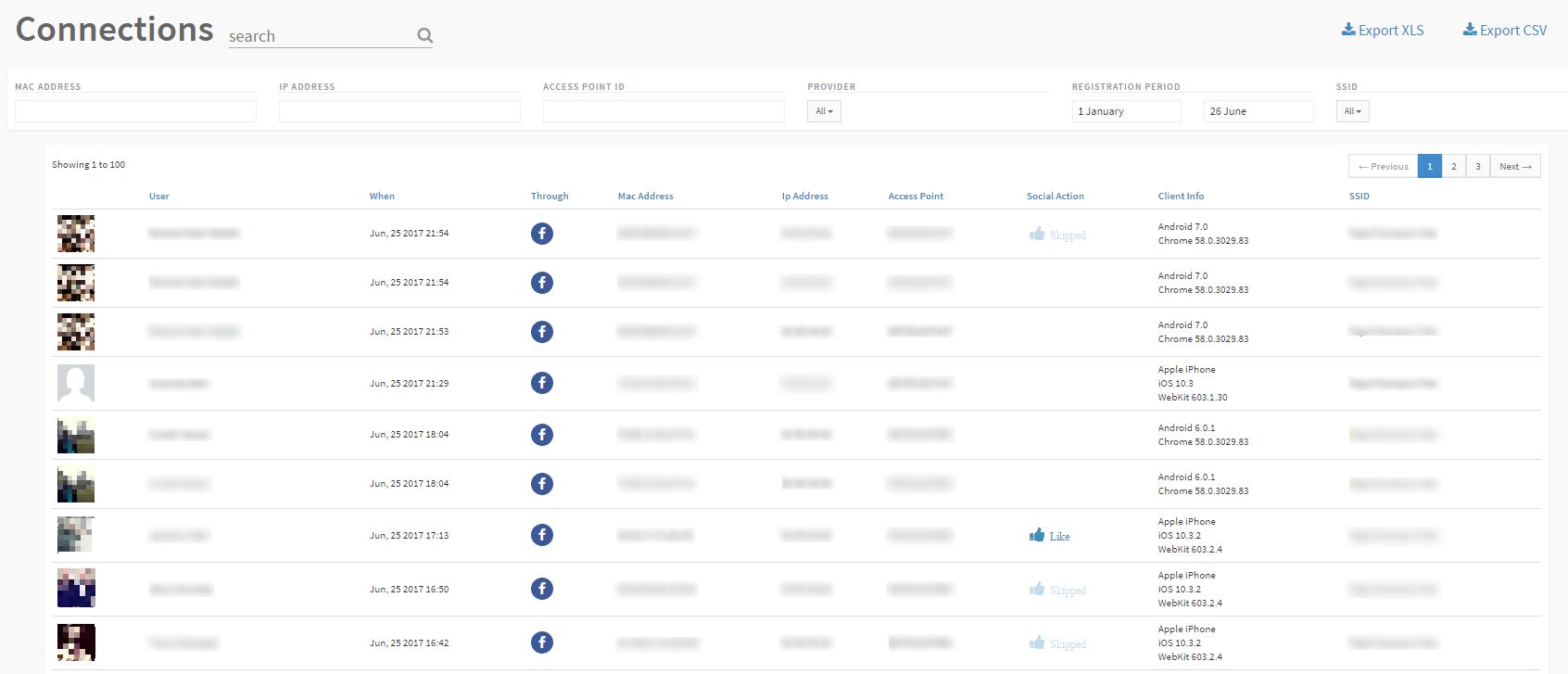
Why does it matter? This twofold kind of information helps you to understand better how the user authentication process to your Wi-Fi network works and the source of some related issues. For instance, visualizing a client in the list of connected clients on the Tanaza Cloud Platform, but not on the analytics dashboard, allows you to know that that user is in the process of authenticating, but didn’t provide his credentials to access Internet yet. Also, Tanaza can help you to detect potential network issues. The following screenshot shows an example of a connected client: here you can see the signal strength. If this element is red, for instance, it means that the user may have problems in reaching your captive portal due to a weak wireless signal, or that he may experience slow WiFi. The best choice in this case is to add one more access point to your network, in order to provide a stronger signal.
Typical use case: any business who wants users to register to their networks, i.e. shopping malls, hotels, schools, etc.
Read our case studies to see how our partners leverage Tanaza Wi-Fi in many different sectors.
Click-through login page
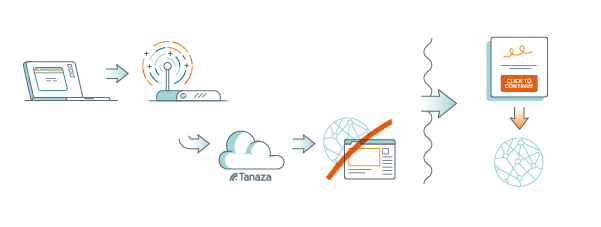
When you configure a click-through login page for user registration, clients authenticate to your network by simply clicking on a button, without providing any personal data. In this case, the authentication process starts once users click on the button and are redirected to the captive portal before accessing the Internet. When the cloud receives users’ request, it notifies the access point of the network that users have authenticated. Now, the access point clears away the captive portal on clients’ devices, and users can fully access Internet. The screenshot below shows how connected clients appear on the Tanaza dashboard: compared to the previous example, you can see more information about clients, as they have successfully authenticated on the captive portal, although in this case no personal data is available.
Read this article to know how the Tanaza Analytics Dashboard works.
Typical use case: the click-through login method is favored by companies with an advertising-based business model, which value clicks for their ads and do not need any other personal data the clientele. Usually, network admins add videos, ads and banners on the login page, so as to further emphasise and advertise their products on the captive portal.
Other login methods: social login
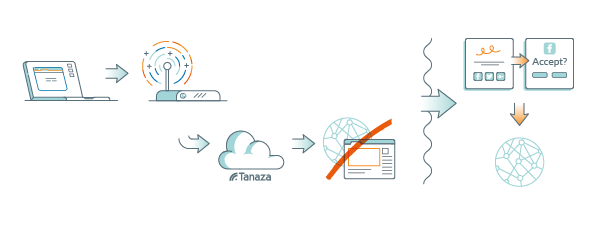
Tanaza features a broad range of authentication methods within its captive portal, i.e. access through email or phone, voucher-based authentication, registration by filling a form and authentication using social networks, aka social login. Lately, the extensive use of social media among people led to the spread of social login among the different user login methods adopted by businesses. In this way, users can connect to an SSID using Facebook, Twitter, Instagram, Linkedin, etc. In this case, user authentication is completed when the login flow through social networks ends, meaning when the user accepts the terms and conditions requested by the social network, i.e. Facebook. The cloud then receives the user device’s request and notifies the access point of the network that the client has authenticated. At this point, full network access is granted. The following screenshot shows the Tanaza dashboard containing a connected client, who authenticated through the social login provided by Tanaza using his Twitter account.
Typical use case: any business whose goal is to boost its social visibility and increase its brand awareness leveraging the power of social media. A bar, for instance, could ask its visitors to like its Facebook page or to share their position to gain more visibility among other Facebook users. Also, a well-working wifi enhances the possibilities to gain positive reviews about your business on websites like TripAdvisor and Yelp.
Read these instructions to learn how to setup a Tanaza built-in login page with social login.

